CVE-2026-28391: OpenClaw Command Injection - The Day I Hacked Myself
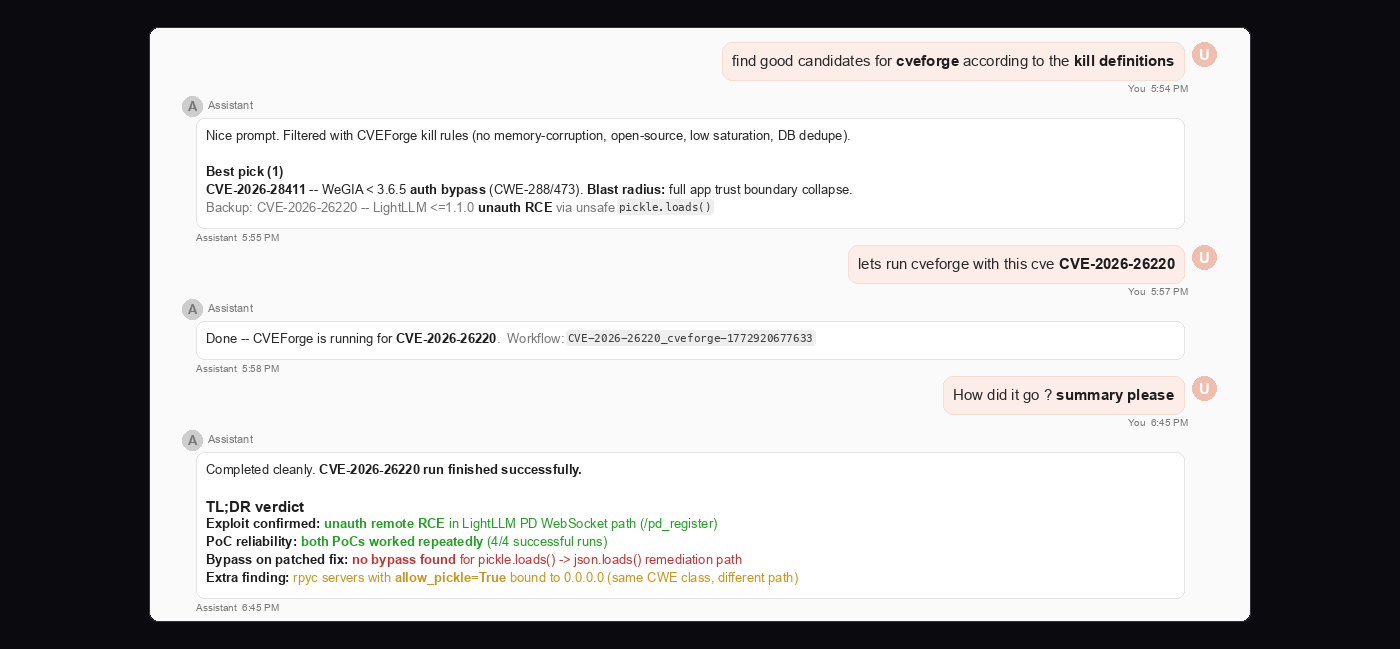
CVE-2026-28391 is a CVSS 9.8 command injection in OpenClaw < 2026.2.2, caused by a POSIX vs cmd.exe shell-parsing mismatch. Our own suggestion algorithm ranked it as the most interesting CVEForge target. 8/8 bypass vectors confirmed, code execution verified. This is the story of the day our orchestration layer dispatched a full vulnerability assessment against itself.