Description
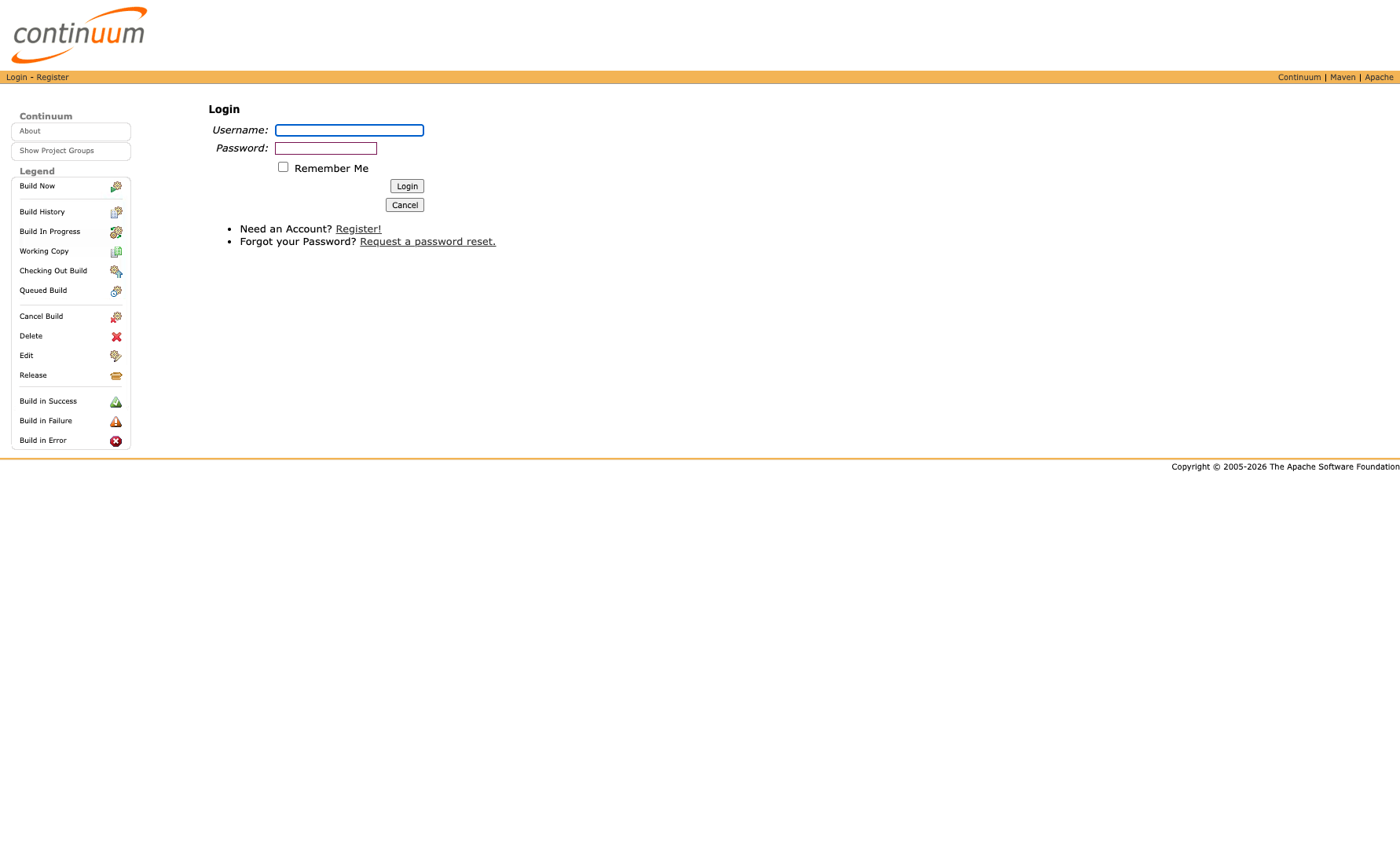
** UNSUPPORTED WHEN ASSIGNED ** Improper Neutralization of Special Elements used in a Command ('Command Injection') vulnerability in Apache Continuum. This issue affects Apache Continuum: all versions. Attackers with access to the installations REST API can use this to invoke arbitrary commands on the server. As this project is retired, we do not plan to release a version that fixes this issue. Users are recommended to find an alternative or restrict access to the instance to trusted users. NOTE: This vulnerability only affects products that are no longer supported by the maintainer.
Exploits (1)
github
WORKING POC
1 stars
by exploitintel · pythonpoc
https://github.com/exploitintel/eip-pocs-and-cves/tree/main/CVE-2016-15057
References (2)
Related Analysis
Scores
CVSS v3
9.9
EPSS
0.2889
EPSS Percentile
96.6%
Attack Vector
NETWORK
CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:C/C:H/I:H/A:H
Lab Environment
Details
VulnCheck KEV
2026-01-26
CWE
CWE-77
Status
published
Products (2)
apache/continuum
org.apache.continuum/continuum
0Maven
Published
Jan 26, 2026
Tracked Since
Feb 18, 2026