Description
The Ruby SAML library is for implementing the client side of a SAML authorization. Ruby-SAML in <= 12.2 and 1.13.0 <= 1.16.0 does not properly verify the signature of the SAML Response. An unauthenticated attacker with access to any signed saml document (by the IdP) can thus forge a SAML Response/Assertion with arbitrary contents. This would allow the attacker to log in as arbitrary user within the vulnerable system. This vulnerability is fixed in 1.17.0 and 1.12.3.
Exploits (2)
github
WORKING POC
1 stars
by exploitintel · pythonpoc
https://github.com/exploitintel/eip-pocs-and-cves/tree/main/CVE-2024-45409
Nuclei Templates (1)
GitLab - SAML Authentication Bypass
CRITICALVERIFIEDby iamnoooob,rootxharsh,pdresearch
Shodan:
http.title:"GitLab"
Scores
CVSS v3
10.0
EPSS
0.4242
EPSS Percentile
97.5%
Attack Vector
NETWORK
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:N
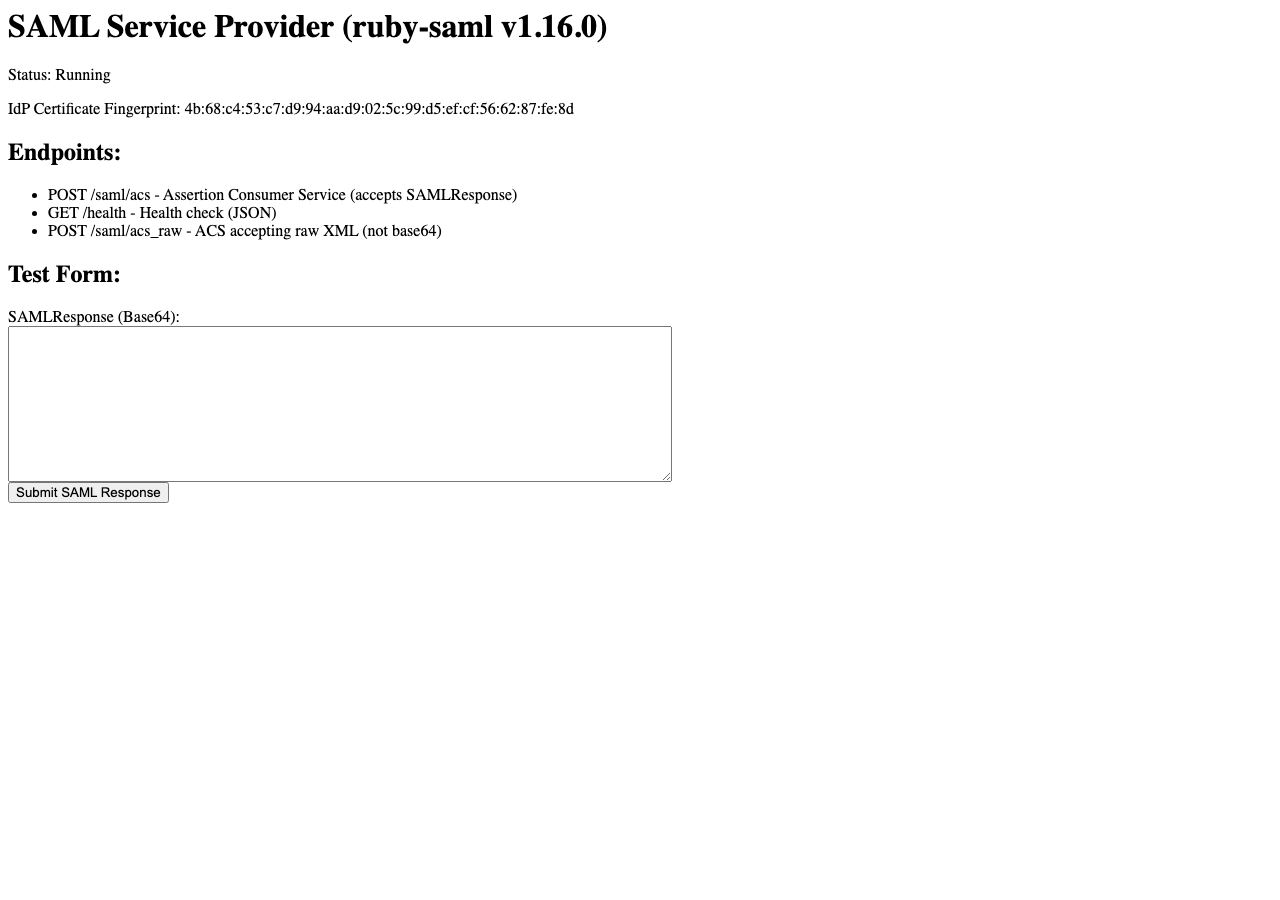
Lab Environment
Details
VulnCheck KEV
2024-10-15
CWE
CWE-347
Status
published
Products (6)
gitlab/gitlab
< 16.11.10
omniauth/omniauth_saml
2.0.0
omniauth/omniauth_saml
2.1.0
omniauth/omniauth_saml
< 1.10.3
onelogin/ruby-saml
< 1.12.3
rubygems/ruby-saml
0 - 1.12.3RubyGems
Published
Sep 10, 2024
Tracked Since
Feb 18, 2026