Description
A remote code execution vulnerability exists where a malicious Raft node can exploit insecure Hessian deserialization within the PD store. The fix enforces IP-based authentication to restrict cluster membership and implements a strict class whitelist to harden the Hessian serialization process against object injection attacks. Users are recommended to upgrade to version 1.7.0, which fixes the issue.
Exploits (1)
github
WORKING POC
1 stars
by exploitintel · pythonpoc
https://github.com/exploitintel/eip-pocs-and-cves/tree/main/CVE-2025-26866
References (3)
Related Analysis
Scores
CVSS v3
8.8
EPSS
0.0241
EPSS Percentile
85.1%
Attack Vector
NETWORK
CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H
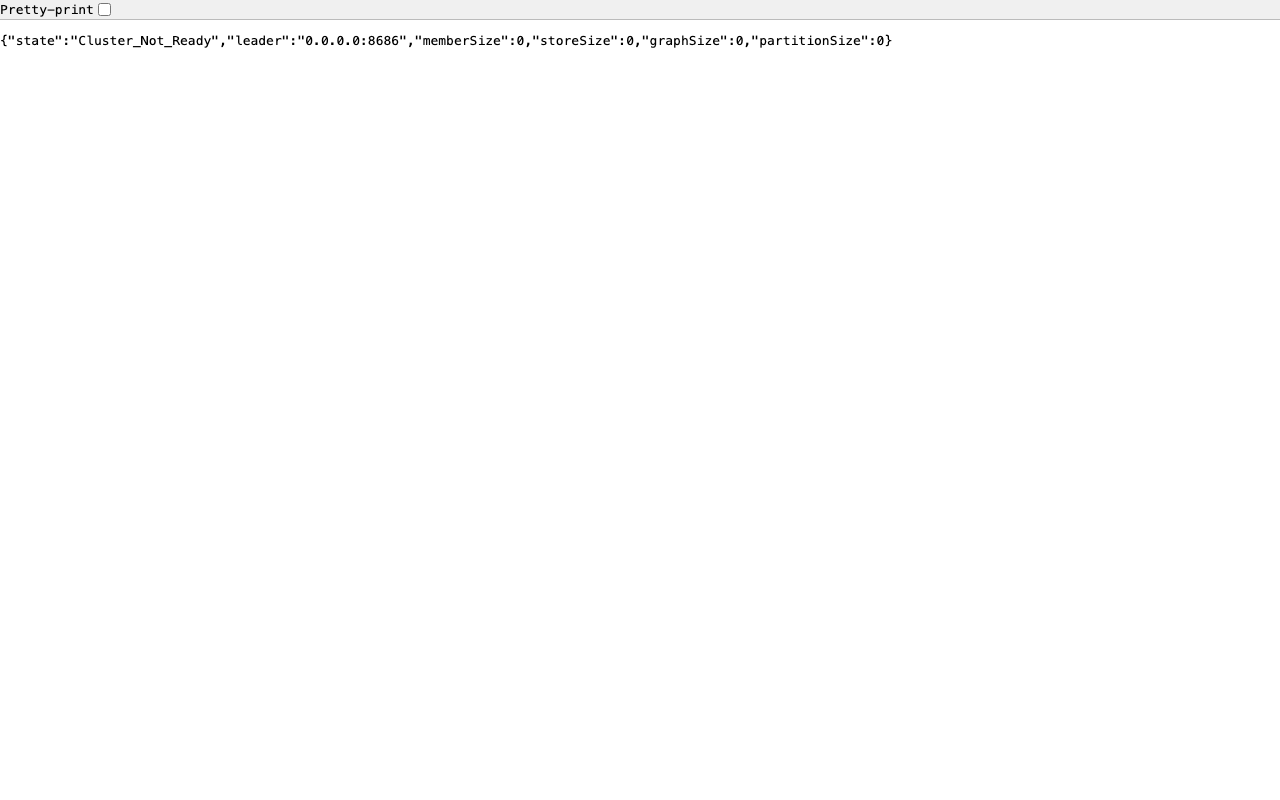
Lab Environment
Details
CWE
CWE-502
Status
published
Products (2)
apache/hugegraph
1.0.0 - 1.7.0
org.apache.hugegraph/hg-pd-core
0 - 1.7.0Maven
Published
Dec 12, 2025
Tracked Since
Feb 18, 2026