Description
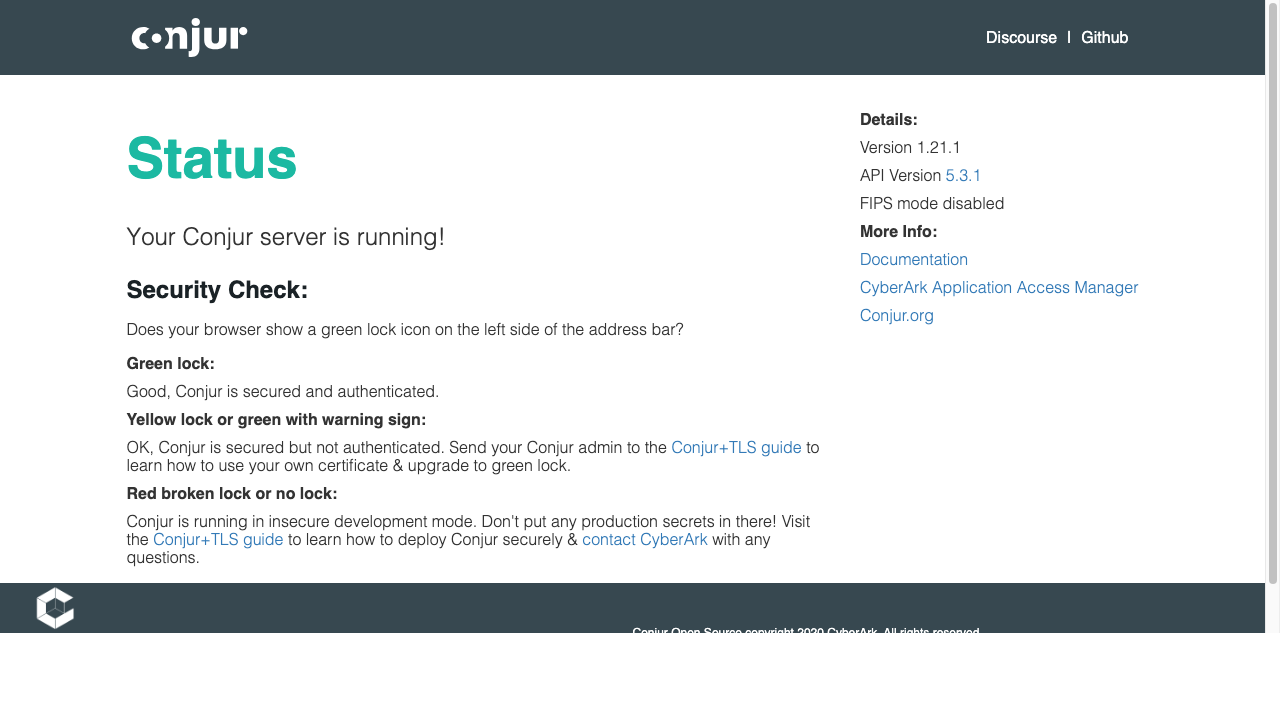
Conjur provides secrets management and application identity for infrastructure. Conjur OSS versions 1.19.5 through 1.21.1 and Secrets Manager, Self-Hosted (formerly known as Conjur Enterprise) 13.1 through 13.4.1 are vulnerable to remote code execution An authenticated attacker who can inject secrets or templates into the Secrets Manager, Self-Hosted database could take advantage of an exposed API endpoint to execute arbitrary Ruby code within the Secrets Manager process. This issue affects both Secrets Manager, Self-Hosted (formerly Conjur Enterprise) and Conjur OSS. Conjur OSS version 1.21.2 and Secrets Manager, Self-Hosted version 13.5 fix the issue.
Exploits (1)
github
WORKING POC
1 stars
by exploitintel · pythonpoc
https://github.com/exploitintel/eip-pocs-and-cves/tree/main/CVE-2025-49828
References (4)
Scores
CVSS v3
8.8
EPSS
0.0030
EPSS Percentile
52.9%
Attack Vector
NETWORK
CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H
Lab Environment
Details
CWE
CWE-1336
Status
published
Products (2)
cyberark/conjur
1.20.1 - 1.21.2
cyberark/conjur
13.1 - 13.5
Published
Jul 15, 2025
Tracked Since
Feb 18, 2026