Description
Cal.com is open-source scheduling software. Prior to 5.9.8, A flaw in the login credentials provider allows an attacker to bypass password verification when a TOTP code is provided, potentially gaining unauthorized access to user accounts. This issue exists due to problematic conditional logic in the authentication flow. This vulnerability is fixed in 5.9.8.
Exploits (1)
github
WORKING POC
1 stars
by exploitintel · pythonpoc
https://github.com/exploitintel/eip-pocs-and-cves/tree/main/CVE-2025-66489
References (1)
Related Analysis
Scores
CVSS v3
9.8
EPSS
0.0017
EPSS Percentile
38.6%
Attack Vector
NETWORK
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H
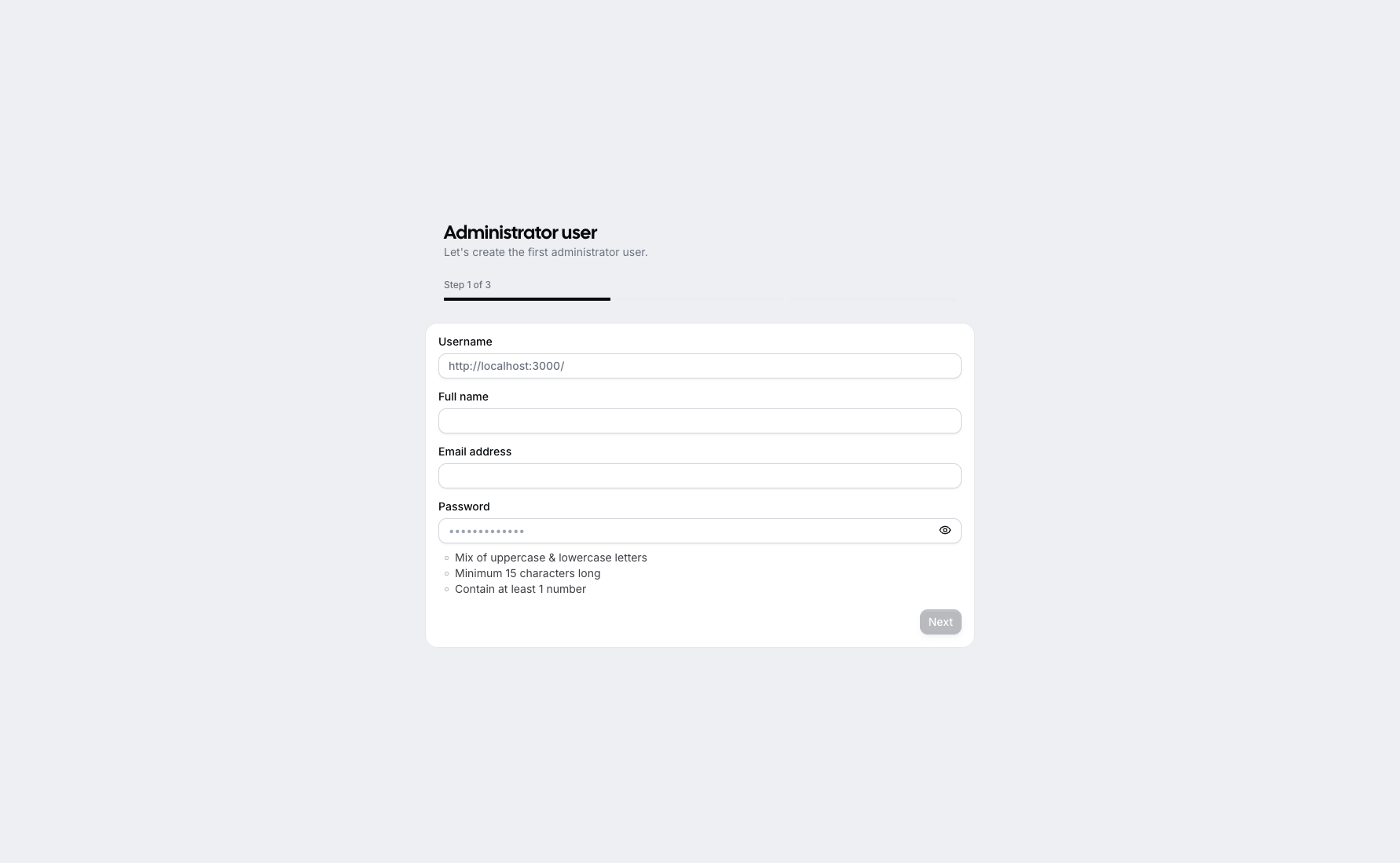
Lab Environment
Details
CWE
CWE-303
Status
published
Products (1)
cal/cal.com
< 5.9.8
Published
Dec 03, 2025
Tracked Since
Feb 18, 2026