Description
OpenClaw is a personal AI assistant. Prior to OpenClaw version 2026.2.14, the Feishu extension previously allowed `sendMediaFeishu` to treat attacker-controlled `mediaUrl` values as local filesystem paths and read them directly. If an attacker can influence tool calls (directly or via prompt injection), they may be able to exfiltrate local files by supplying paths such as `/etc/passwd` as `mediaUrl`. Upgrade to OpenClaw `2026.2.14` or newer to receive a fix. The fix removes direct local file reads from this path and routes media loading through hardened helpers that enforce local-root restrictions.
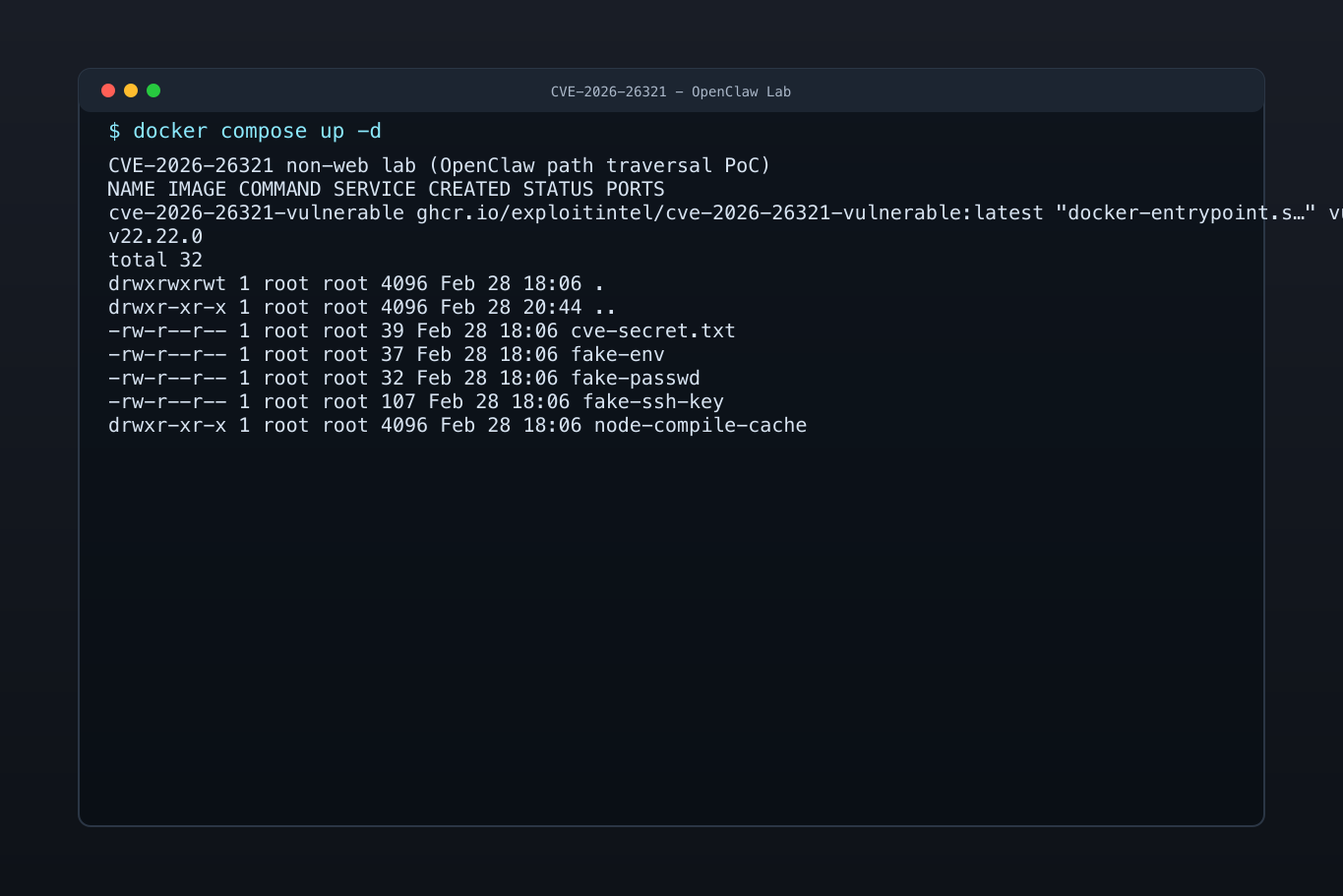
Exploits (1)
github
WORKING POC
1 stars
by exploitintel · pythonpoc
https://github.com/exploitintel/eip-pocs-and-cves/tree/main/CVE-2026-26321
References (3)
Related Analysis
Scores
CVSS v3
7.5
EPSS
0.0003
EPSS Percentile
7.6%
Attack Vector
NETWORK
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N
Lab Environment
Details
CWE
CWE-22
Status
published
Products (2)
npm/openclaw
0 - 2026.2.14npm
openclaw/openclaw
< 2026.2.14
Published
Feb 19, 2026
Tracked Since
Feb 20, 2026