Description
MLflow Use of Default Password Authentication Bypass Vulnerability. This vulnerability allows remote attackers to bypass authentication on affected installations of MLflow. Authentication is not required to exploit this vulnerability. The specific flaw exists within the basic_auth.ini file. The file contains hard-coded default credentials. An attacker can leverage this vulnerability to bypass authentication and execute arbitrary code in the context of the administrator. Was ZDI-CAN-28256.
Exploits (1)
github
WORKING POC
1 stars
by exploitintel · pythonpoc
https://github.com/exploitintel/eip-pocs-and-cves/tree/main/CVE-2026-2635
References (2)
Related Analysis
Scores
CVSS v3
9.8
EPSS
0.0109
EPSS Percentile
77.9%
Attack Vector
NETWORK
CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H
Lab Environment
Details
CWE
CWE-1393
Status
published
Products (2)
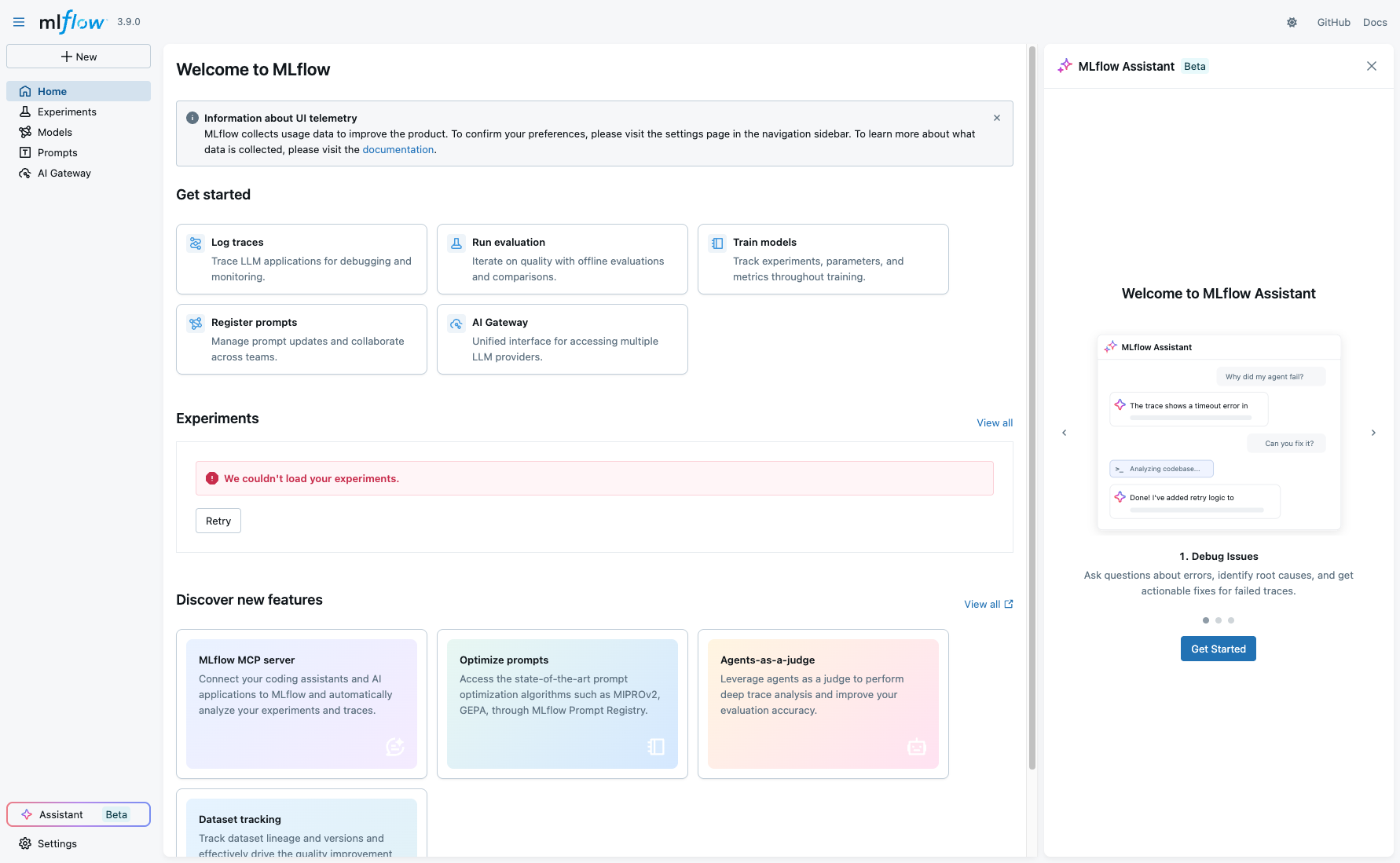
MLflow/MLflow
3.4.0
pypi/mlflow
0 - 3.8.0rc0PyPI
Published
Feb 20, 2026
Tracked Since
Feb 21, 2026