Description
Vim is an open source, command line text editor. Prior to version 9.2.0073, an OS command injection vulnerability exists in the `netrw` standard plugin bundled with Vim. By inducing a user to open a crafted URL (e.g., using the `scp://` protocol handler), an attacker can execute arbitrary shell commands with the privileges of the Vim process. Version 9.2.0073 fixes the issue.
Exploits (1)
github
WORKING POC
1 stars
by exploitintel · pythonpoc
https://github.com/exploitintel/eip-pocs-and-cves/tree/main/CVE-2026-28417
References (4)
Related Analysis
Scores
CVSS v3
4.4
EPSS
0.0001
EPSS Percentile
1.9%
Attack Vector
LOCAL
CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:L/I:L/A:N
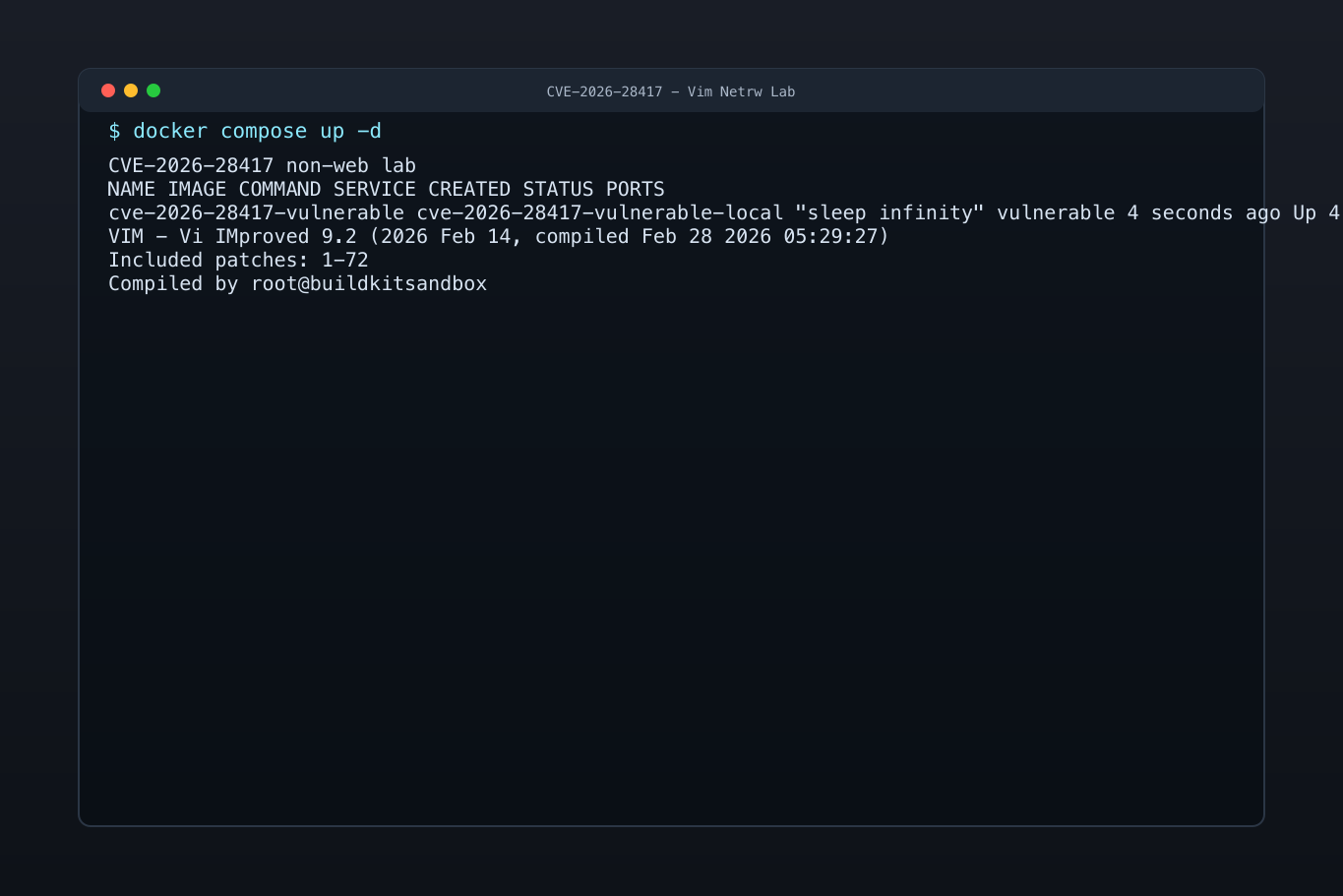
Lab Environment
Details
CWE
CWE-78
CWE-86
Status
published
Products (1)
vim/vim
< 9.2.0073
Published
Feb 27, 2026
Tracked Since
Feb 28, 2026