Pi-hole Web Interface has a Command Injection Vulnerability
Title source: cnaDescription
Pi-hole Admin Interface is a web interface for managing Pi-hole, a network-level ad and internet tracker blocking application. Versions prior to 6.0 have a critical OS Command Injection vulnerability in the savesettings.php file. The application takes the user-controlled $_POST['webtheme'] parameter and concatenates it directly into a system command executed via PHP's exec() function. Since the input is neither sanitized nor validated before being passed to the shell, an attacker can append arbitrary system commands to the intended pihole command. Furthermore, because the command is executed with sudo privileges, the injected commands will run with elevated (likely root) privileges. Version 6.0 patches the issue.
Exploits (1)
github
WORKING POC
3 stars
by exploitintel · cpoc
https://github.com/exploitintel/eip-pocs-and-cves/tree/main/CVE-2026-33765
Scores
CVSS v3
9.8
EPSS
0.0024
EPSS Percentile
47.7%
Attack Vector
NETWORK
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H
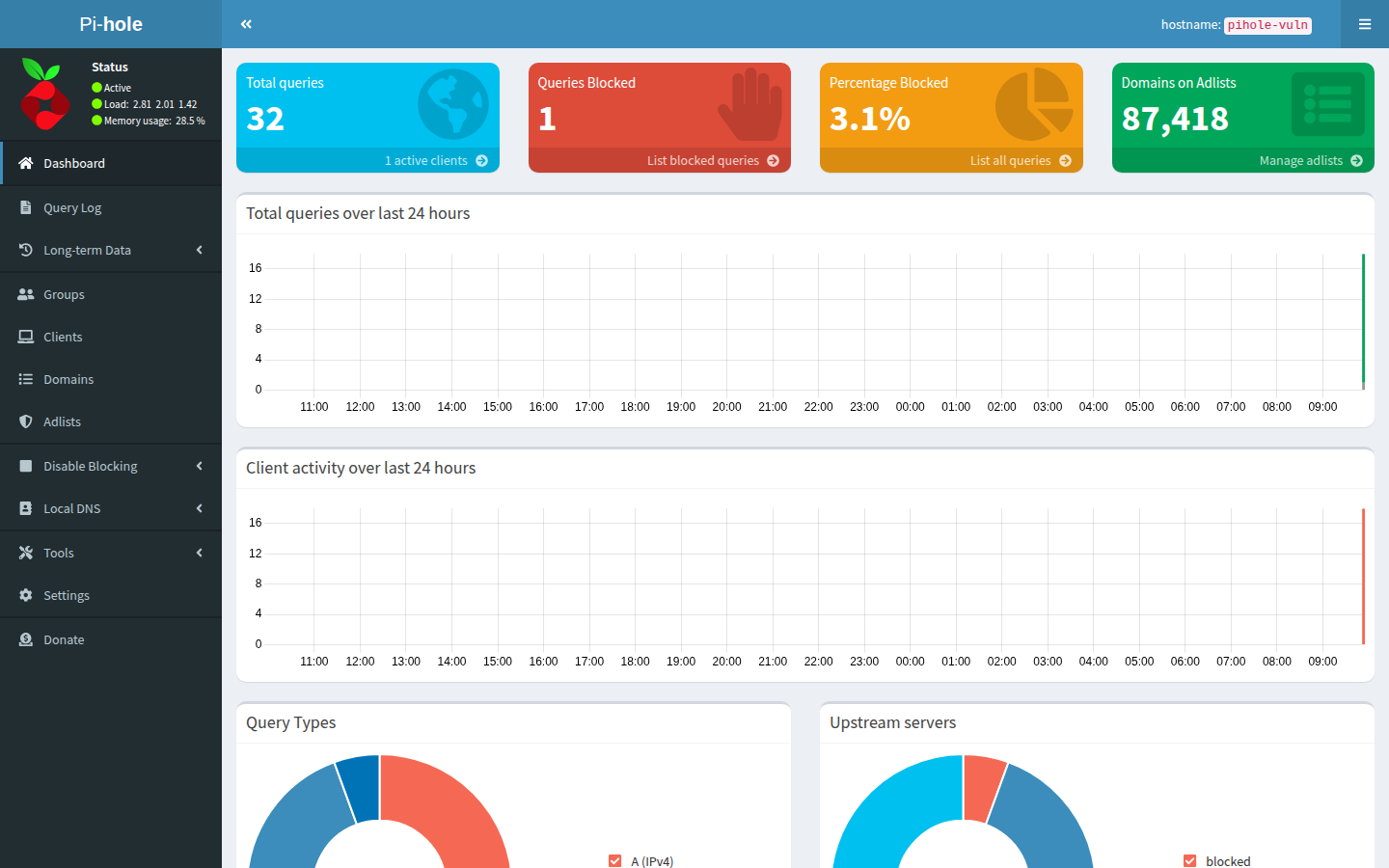
Lab Environment
Details
CWE
CWE-78
Status
published
Products (2)
pi-hole/web
< 6.0
pi-hole/web_interface
< 6.0
Published
Mar 27, 2026
Tracked Since
Mar 29, 2026