Description
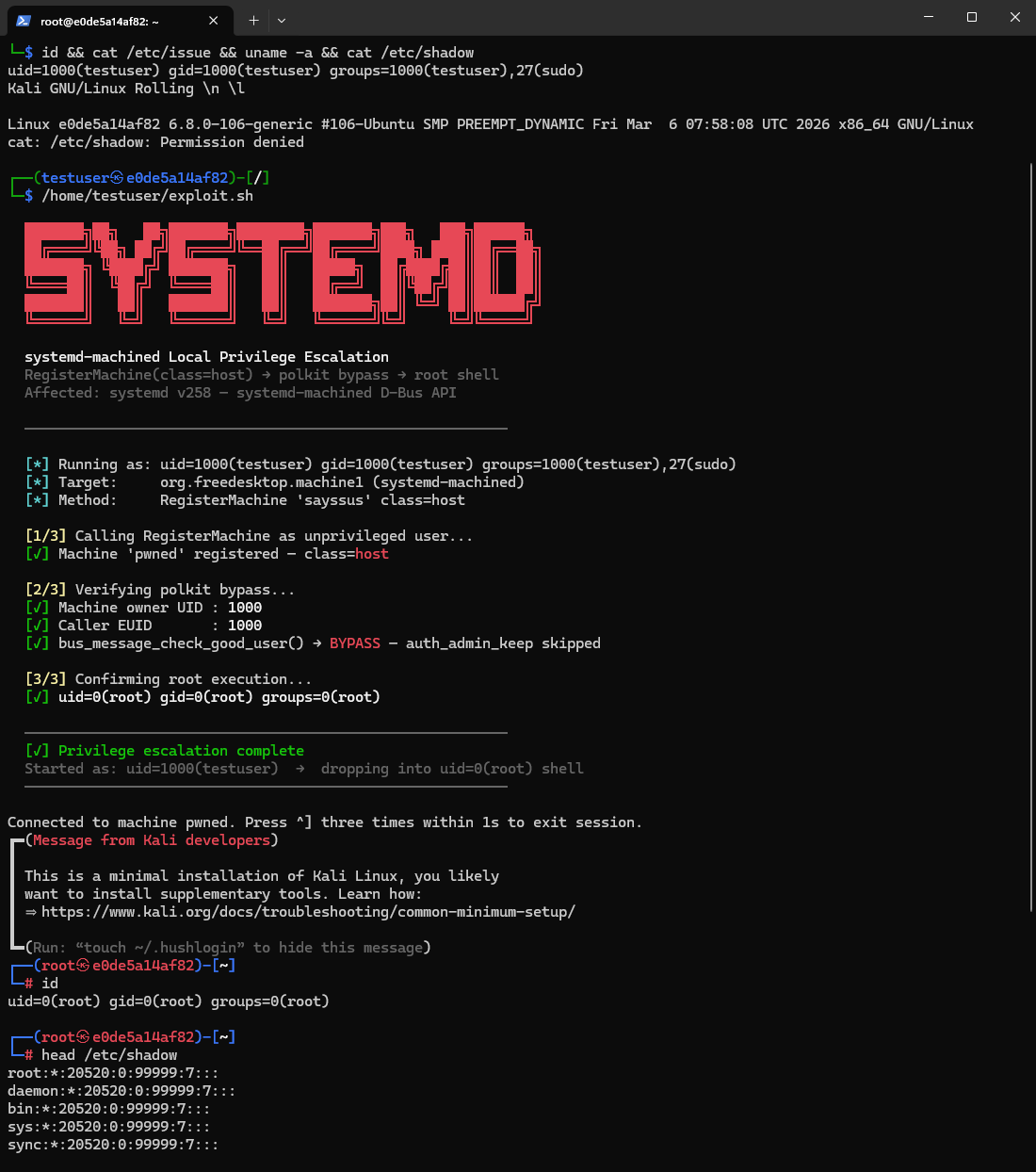
A flaw was found in systemd. The systemd-machined service contains an Improper Access Control vulnerability due to insufficient validation of the class parameter in the RegisterMachine D-Bus (Desktop Bus) method. A local unprivileged user can exploit this by attempting to register a machine with a specific class value, which may leave behind a usable, attacker-controlled machine object. This allows the attacker to invoke methods on the privileged object, leading to the execution of arbitrary commands with root privileges on the host system.
Exploits (1)
github
WORKING POC
2 stars
by exploitintel · cpoc
https://github.com/exploitintel/eip-pocs-and-cves/tree/main/CVE-2026-4105
References (3)
Related Analysis
Scores
CVSS v3
6.7
EPSS
0.0001
EPSS Percentile
1.7%
Attack Vector
LOCAL
CVSS:3.1/AV:L/AC:H/PR:L/UI:R/S:U/C:H/I:H/A:H
CISA SSVC
Vulnrichment
Exploitation
none
Automatable
no
Technical Impact
total
Lab Environment
Details
CWE
CWE-284
Status
published
Products (17)
Red Hat/Red Hat Enterprise Linux 10
NetworkManager
Red Hat/Red Hat Enterprise Linux 10
rpm-ostree
Red Hat/Red Hat Enterprise Linux 10
systemd
Red Hat/Red Hat Enterprise Linux 10
Red Hat/Red Hat Enterprise Linux 7
systemd
Red Hat/Red Hat Enterprise Linux 7
Red Hat/Red Hat Enterprise Linux 8
NetworkManager
Red Hat/Red Hat Enterprise Linux 8
systemd
Red Hat/Red Hat Enterprise Linux 8
Red Hat/Red Hat Enterprise Linux 9
NetworkManager
... and 7 more
Published
Mar 13, 2026
Tracked Since
Mar 14, 2026